How to Install and Configure SSTP VPN with Network Manager, CA Certificates, and Remmina on Ubuntu
In many development and testing environments, secure remote access is a daily requirement. Whether we are connecting to staging servers, internal QA systems, or Windows-based test machines, having a properly configured VPN and remote desktop client is essential.

In this guide, we will walk through:
- Installing the SSTP plugin for Network Manager
- Configuring an SSTP VPN connection (using example placeholders)
- Adding a custom CA certificate to the system trust store
- Installing Remmina with RDP support for Windows access
This tutorial is designed for developers and software testers working on Debian/Ubuntu-based systems who need a reliable and secure setup process.
1. Install SSTP Plugin for Network Manager
Secure Socket Tunneling Protocol (SSTP) is commonly used in enterprise environments because it operates over HTTPS (TCP port 443), making it firewall-friendly and secure.
Ubuntu’s Network Manager supports SSTP through a dedicated plugin.
Step 1: Update Package Index
sudo apt update
Keeping the package list updated ensures we install the latest available version.
Step 2: Install the SSTP Plugin
sudo apt install network-manager-sstp
This package enables SSTP VPN support directly inside the Network Manager graphical interface.
What Gets Installed
- SSTP protocol support
- PPP dependencies
- Integration with GNOME network settings
If the SSTP option does not immediately appear, logging out and back in (or restarting Network Manager) usually resolves it.
2. Configure the SSTP VPN Connection
After installation, we configure the VPN using Ubuntu’s graphical interface.
Step-by-Step Configuration
- Click the network icon in the top-right corner.
- Go to Settings → Network → VPN.
- Click Add VPN.
- Choose Secure Socket Tunneling Protocol (SSTP).
Now enter the VPN details using placeholders provided by your organization:
- Gateway:
203.0.113.10 - Username:
dev_user - Password:
your_password_here - Leave other settings as default unless instructed otherwise.
The gateway and username above are examples. Always use credentials provided by your infrastructure or IT team.
Click Add to save the configuration.
3. Connect to the SSTP VPN
To initiate the connection:
- Click the network icon.
- Navigate to VPN Connections.
- Select your configured SSTP connection.
If successful, the VPN will establish within a few seconds.
Verify the Connection
We can verify the VPN interface:
ip a
Look for a ppp interface.
We can also check our public IP:
curl ifconfig.me
If connected, the IP address should reflect the VPN network.
4. Copy CA Certificate to System Trust Store
In many corporate environments, VPN servers use custom Certificate Authorities (CAs). Without trusting this CA, TLS validation may fail.
To fix this, we add the CA certificate to the system trust store.
Step 1: Copy the Certificate
sudo cp your_certificate.crt /usr/local/share/ca-certificates/your_certificate.crt
Place the certificate in the recommended directory for local CAs.
Step 2: Update the Trust Store
sudo update-ca-certificates
This command:
- Scans for
.crtfiles - Updates system certificates
- Makes the CA trusted across the OS
Why This Is Important
After updating:
- Network Manager can validate VPN certificates
- Tools like
curl,git, andwgettrust internal HTTPS services - We avoid TLS and SSL verification errors
5. Install Remmina with RDP Plugin (For Windows Access)
Many QA and development workflows require connecting to Windows servers. Remmina is a flexible remote desktop client that supports RDP.
Install Remmina and RDP Plugin
sudo apt install remmina remmina-plugin-rdp -y
This installs:
- The Remmina client
- RDP support for Windows remote access
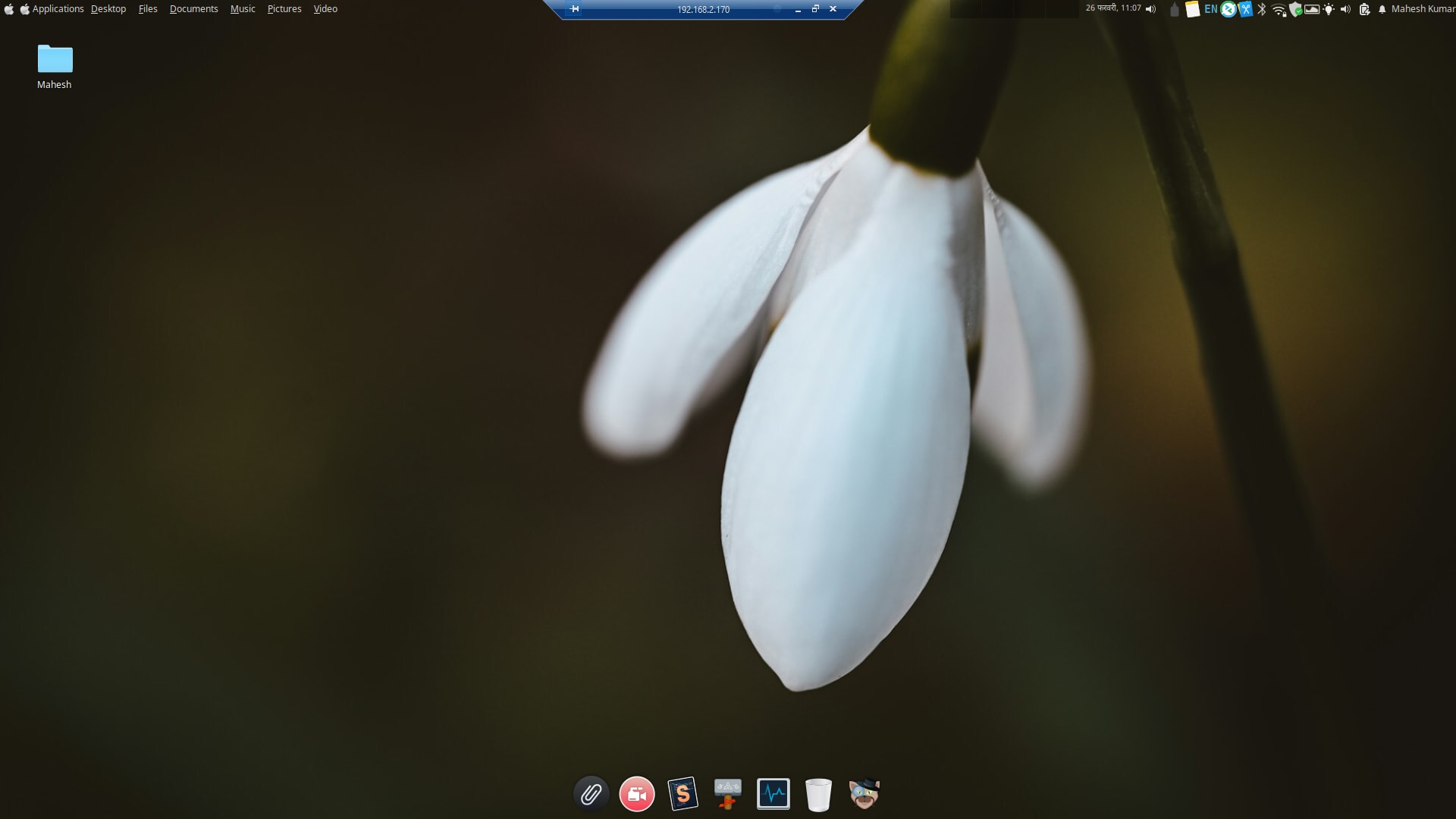
6. Connect to a Windows Machine via RDP
After installation:
- Open Remmina.
- Click + to create a new connection profile.
- Select RDP - Remote Desktop Protocol.
-
Enter:
- Server IP (e.g.,
192.0.2.25) - Username
- Password
- Server IP (e.g.,
- Save and connect.
Best Practices for Development Teams
- Use descriptive connection names (e.g.,
QA-WIN-SERVER) - Save credentials securely
- Disable unnecessary features (like sound redirection) to reduce bandwidth
- Use lower color depth if performance is an issue
Troubleshooting Common Issues
VPN Fails to Connect
- Verify gateway address
- Confirm credentials
-
Check connectivity:
nc -zv 203.0.113.10 443 -
Inspect logs:
journalctl -u NetworkManager
Certificate Errors
- Ensure the file ends with
.crt - Re-run
sudo update-ca-certificates - Confirm the correct certificate was provided
RDP Displays Black Screen
- Lower color depth
- Disable hardware acceleration
- Confirm Windows RDP is enabled
Conclusion
By installing the SSTP plugin for Network Manager, configuring a secure VPN connection with placeholder credentials, trusting the required CA certificate, and installing Remmina with RDP support, we establish a reliable remote-access environment on Ubuntu.
This setup allows us to:
- Securely access internal networks
- Avoid TLS certificate issues
- Connect to Windows test machines
- Maintain a consistent development workflow
With this configuration in place, our Linux system becomes a secure and productive gateway into enterprise infrastructure—ready for development, testing, and remote administration tasks.




Leave a comment