How We Install and Configure SSTP VPN and RDP Access on Ubuntu for Secure Development
In many development and QA environments, secure remote access is not optional—it is foundational. Whether we are accessing internal staging servers, Windows-based test environments, or isolated enterprise networks, we often rely on a VPN connection combined with Remote Desktop Protocol (RDP).
In this guide, we walk through how we:
- Install the SSTP plugin for Network Manager on Ubuntu
- Configure an SSTP VPN connection
- Add a custom CA certificate to the system trust store
- Install and enable XRDP for Windows RDP compatibility
This tutorial is written for developers and software testers who need secure, repeatable setup steps that work in real-world environments.
1. Installing the SSTP Plugin for Network Manager
Secure Socket Tunneling Protocol (SSTP) is commonly used in enterprise VPN environments because it runs over HTTPS (TCP 443), making it firewall-friendly and secure.
On Ubuntu systems using NetworkManager, we need to install the SSTP plugin.
Step 1: Update Package Lists
sudo apt update
Keeping package indexes updated ensures we install the latest compatible version.
Step 2: Install the SSTP Plugin
sudo apt install network-manager-sstp
This installs:
- The SSTP VPN plugin
- Required PPP components
- Integration with NetworkManager GUI
Once installed, the SSTP option becomes available in the VPN configuration interface.
2. Configuring the SSTP VPN Connection
After installing the plugin, we configure the VPN through the graphical interface.
Step-by-Step Configuration
- Click the network icon in the top-right corner.
- Open Settings.
- Navigate to Network → VPN.
- Click Add VPN.
- Select Secure Socket Tunneling Protocol (SSTP).
Now we fill in the connection details:
- Gateway:
110.44.119.178 - Username:
mahesh - Password: (enter provided password)
- Leave other settings as default.
Click Add to save the configuration.
Best Practices
When setting up VPN credentials in development environments, we recommend:
- Storing credentials securely using GNOME Keyring
- Avoiding hardcoded credentials in scripts
- Verifying gateway IP addresses with infrastructure teams
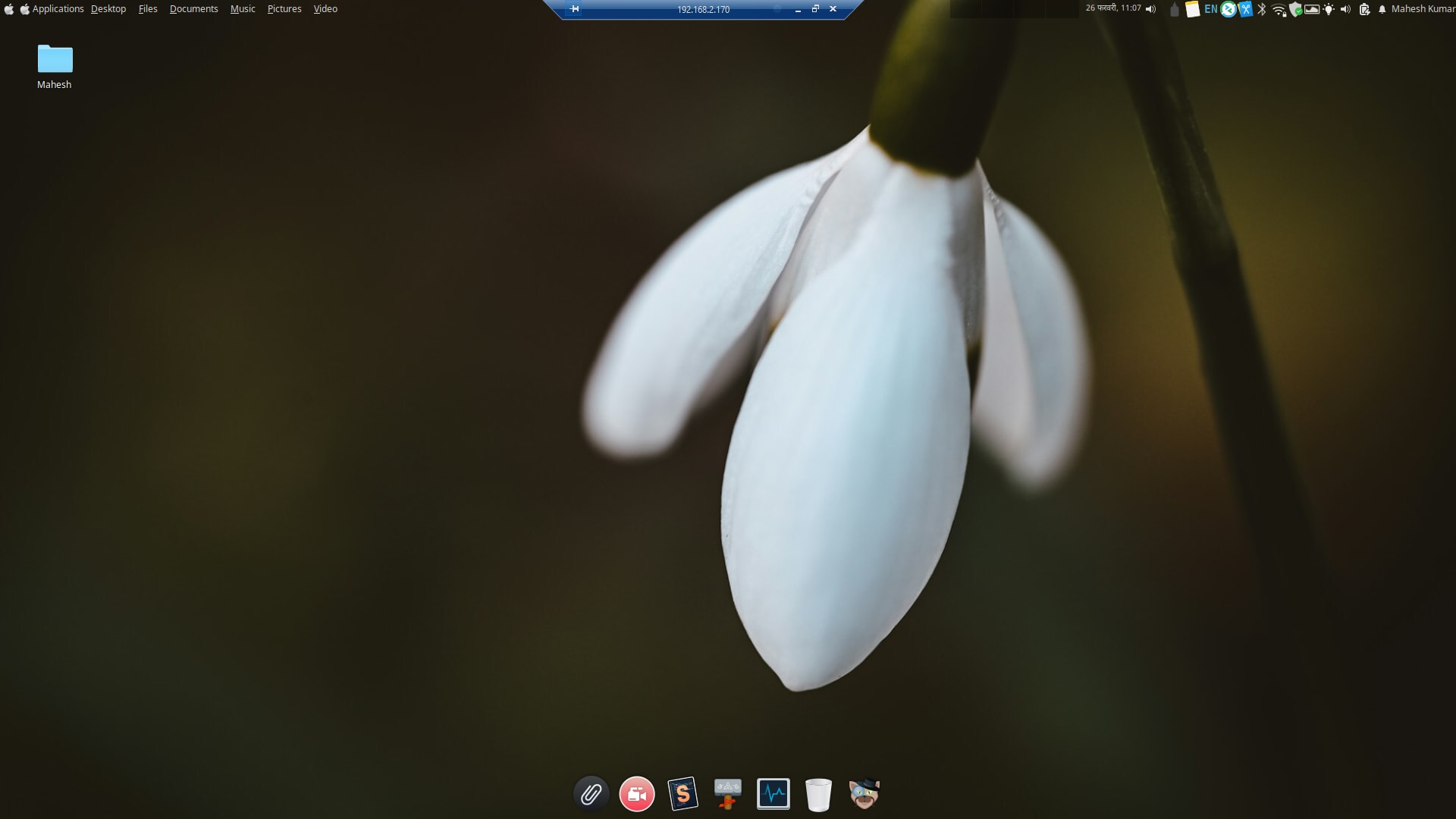
3. Connecting to the SSTP VPN
After configuration, connecting is straightforward:
- Click the network icon
- Select VPN Connections
- Choose the configured SSTP connection
If successful, we should see:
- A VPN indicator in the top panel
- An assigned internal IP (verify using
ip a)
ip a
This confirms that the tunnel interface is active.
4. Copying a CA Certificate to the System Trust Store
In many enterprise setups, VPN servers use certificates signed by an internal Certificate Authority (CA). If the CA is not trusted by our system, the VPN connection may fail.
To resolve this, we add the CA certificate to Ubuntu’s trust store.
Step 1: Copy the Certificate
sudo cp your_certificate.crt /usr/local/share/ca-certificates/your_certificate.crt
We place the certificate in:
/usr/local/share/ca-certificates/
This directory is intended for locally trusted CAs.
Step 2: Update the CA Store
sudo update-ca-certificates
This rebuilds the system certificate bundle and includes our custom CA.
Verification Tip
We can confirm the certificate was added successfully by reviewing the output of the update command. It should indicate that one certificate was added.
5. Installing and Enabling RDP Support (XRDP)
Once connected to the VPN, we often need to access Windows-based environments or allow remote desktop access to our Ubuntu machine.
We use XRDP, an open-source implementation of Microsoft’s RDP protocol.
Install XRDP
sudo apt install xrdp -y
Enable and Start XRDP
sudo systemctl enable --now xrdp
This ensures:
- XRDP starts immediately
- XRDP starts automatically on boot
Allow RDP Through Firewall
If UFW (Uncomplicated Firewall) is enabled:
sudo ufw allow from any to any port 3389 proto tcp
Port 3389 is the default RDP port.
6. Verifying the Setup
After completing all steps, we should validate:
✅ VPN Status
- VPN icon visible
ip ashows tunnel interface
✅ Certificate Trust
- No TLS/certificate errors during connection
✅ XRDP Service
sudo systemctl status xrdp
✅ RDP Port Listening
sudo ss -tulnp | grep 3389
This confirms the service is actively listening.
Common Issues and Troubleshooting
VPN Fails to Connect
Possible causes:
- Incorrect gateway IP
- Wrong credentials
- Missing CA certificate
- Firewall blocking outbound HTTPS
Certificate Errors
- Ensure
.crtextension is used - Confirm correct directory path
- Re-run
update-ca-certificates
RDP Connection Refused
- Verify XRDP is running
- Confirm firewall rule is applied
- Check that port 3389 is not blocked by cloud security groups
Why This Setup Matters for Development Teams
For development and QA workflows, this configuration enables:
- Secure access to internal staging systems
- Remote debugging inside enterprise networks
- Cross-platform testing (Linux to Windows)
- Safe communication over encrypted tunnels
By standardizing this process, we reduce onboarding time and minimize environment-related blockers.
Conclusion
In this guide, we walked through how we:
- Installed the SSTP plugin for Network Manager
- Configured a secure VPN connection
- Trusted a custom CA certificate
- Installed and enabled XRDP for RDP access
These steps form a reliable foundation for secure remote development and testing environments on Ubuntu.
When implemented correctly, this setup provides a stable, encrypted, and production-ready access workflow that scales across teams.
By documenting and standardizing this configuration, we ensure our development environments remain secure, reproducible, and efficient.





Leave a comment